Fachbereich Physik
Foto: UHH/Ohme
Fachbereich Physik
Foto: FB Physik / Wenig
Fachbereich Physik
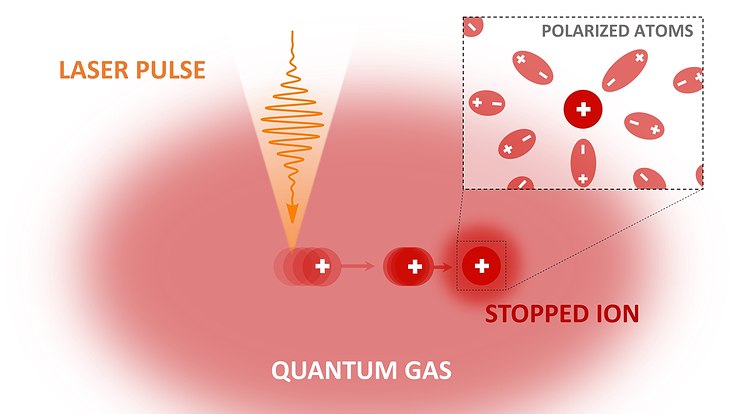
Laserphysik und Photonik
Foto: FB Physik/M. Brüggen
Fachbereich Physik
Elementarteilchen- und Astrophysik
Foto: FB Physik/J. Wiebe
Fachbereich Physik
Festkörper- und Nanostrukturphysik
Foto: Unsplash
Solidarität mit der Ukraine
Wir schließen uns dem Statement der Allianz der Wissenschaftsorganisationen an